Veritas NetBackup Isolated Recovery Environment – Your answer to Ransomware
In this article
This article was written by Rachel Zhu, Technology Evangelist at Veritas
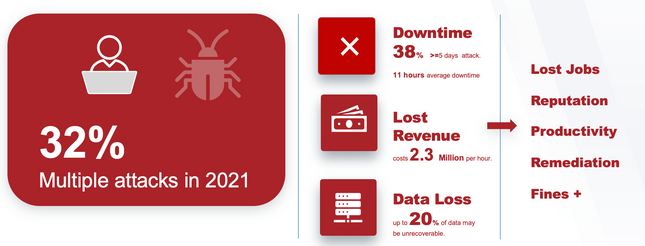
2021 was a record year of ransomware attacks. Researchers observed 623.3 million attacks globally. That is 19 attacks per sec. And those are just the ones that we know about. Ransomware becomes the number 1 priority for the CISOs and CIOs around the world.
According to recent ESG research, backups and backup infrastructure is now a very desirable target for cyber criminals, as they believe that will optimize their chances of getting a ransom from their target. To make matters worse, our research has made it clear that if you have been attacked by ransomware, then you are 32% more likely to be attacked multiple times in the future. The same research showed that the average organization has experienced 2.57 ransomware attacks that led to downtime in the last 12 months, with 14% having been hit five times, or more!
What are the challenges to protect your data from ransomware?
The data is all over the place, and not just geographically, but also spread across multiple providers and in multiple form factors - physical, virtual, cloud, and containers. The data grows exponentially, and the threat actors have a growing set of options from which to attack. 94% of Senior IT Executives say that their security measures have not kept up with complexity.
Ransomware-as-a-Service vendors exist in large numbers and have successfully transitioned to a highly profitable business model with the charter of successfully crippling organizations at their most vulnerable times to maximize ransoms. These RaaS businesses provide turnkey code, have advanced support networks with helplines and provide tools for encryption, communicating with victims and facilitating ransom collection. They are sharing information, knowledge and supporting each other.
It is common practice for bad actors to get into systems and lay dormant to find the most vulnerable places, then they strike at the optimal time to inflict maximum impact.
Combat RaaS with NetBackup Isolated Recovery Environment (IRE)
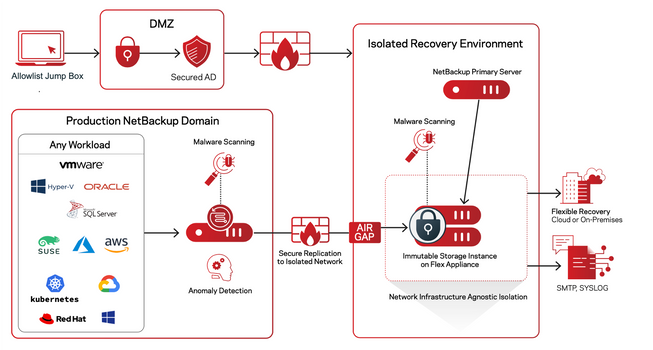
Traditionally the best way to protect data from ransomware attack is to store it in an isolated recovery environment or airgap solution which is disconnected without a physical connection, for example tape-based backups or offsite systems. However, one of the limitations of this is there is no malware detection and you can't recover your data fast or at scale. Unlike traditional IRE solutions, the NetBackup Flex IRE solution offers a unified, scalable solution with immutability and indelibility. Veritas NetBackup IRE aligns to the National Institute of Standards and Technology (NIST) framework with a focus on 3 principles- protect, detect, and recover.
PROTECT - safeguarding data integrity with system hardening, immutability and network isolation.
DETECT - monitoring and reporting on system activity to mitigate threats and vulnerabilities
RECOVER - automating and orchestrating complete cross-system restoration and
non-disruptive rehearsals
Based on these three principles, Veritas has implemented an IRE solution with unparalleled immutability, complete visibility and fast recovery. Veritas NetBackup IRE can provide support for built-in immutability and indelibility, third party hardware immutability, Cloud based locked object storage immutability and immutability for SaaS workload backups. Also, NetBackup can directly send and efficiently store deduplicated data on AWS S3 Object Lock.
Veritas can cross reference data points on your production environment and backup vendors to ensure no system falls through the cracks. This level of visibility is essential for complete protection of your entire environment. We can also send these correlations to third-party detection and response solutions using popular methods.
By combining our backup replication, VM I/O replication, Native array and Database replication in a single orchestration plan, we can efficiently restore all your workloads. The following diagram describes Veritas NetBackup IRE architecture
- Secure your network to use a whitelist jump box to access your IRE environment.
- Guarantee a clean image by malware scanning during and after backup as well as before restoring
- Secure replication by encrypting data both in transit and at rest
- Adopt a Zero Trust security posture across your entire environment
- Immutable Storage
- Optimize for Flexible, Rapid, Hybrid Recovery, At Scale
Veritas has been recognized by analysts for over 15 years as the data protection leader. NetBackup Flex appliances are built with a hardened OS that includes multiple –layers of security enhancements that has a perfect enterprise security track record. The NetBackup IRE is an all-in-one solution with no 3rd-party dependencies and includes backup anomaly scanning that is fully integrated with NetBackup software. Flex appliance Active/Active provides high availability and high performance with 2x throughput and 3x faster backup and restore.

