Key Takeaways From VMware EMPOWER 2022
In this blog
Overview

As an overall experience, virtual technical conferences can be challenging to execute, but VMware did a great job with the delivery. It appeared that most sessions were recorded rather than live, but the platform they used for delivering them was stable and worked well. There seemed to be content for everyone, but as with most technology conferences, it was a struggle to find truly technical sessions that weren't heavily front-loaded with marketing content. Partners can access the content here after you are logged in.
A key takeaway I had across all the sessions I attended was a strong messaging shift from VMware, moving away from classic virtualization and SDDC (Software Defined Data Center) technology talk tracks and more toward application platforms, security and multicloud. It will take a long time to up-skill the classic VMWare partner ecosystem to be able to have these conversations with customers, so I think it's good they're moving in this direction. The tricky part will be finding partners that can handle both the classic and modern needs of customers to help them modernize their infrastructure and digitally transform their people and processes. Fortunately, WWT is one of the few partners that has the scope and scale to meet these needs.
Multicloud messaging
VMware has seemingly tightened its messaging around multicloud. In earlier discussions, there has been a loose definition that led to a lot of overlap between multicloud, hybrid cloud and multiple clouds. During EMPOWER 2022 they focused more on multicloud being the realization of a single application taking advantage of features from multiple clouds. This makes it clear that: 1) multiple clouds are simply different teams doing different things independently in different cloud environments and 2) hybrid cloud is a common SDDC infrastructure spanning public and private clouds.
The session I attended on VCF (VMware Cloud Foundation) focused on extracting more value from the VCF project. VMware and Dell perform a lot of the 'base' services around VCF, and this session talked a lot about the components that go beyond those base deployments as well as how to make sure the value of VCF is exploited. Things that aren't commonly considered like update workflow from an operational playbook perspective were discussed. Also, helping a customer create intelligent patching approaches for VCF based upon CVSS (Common Vulnerability Scoring System) was an interesting idea.

And, of course, there are a lot of components beyond vSAN/NSX/vSphere that are included in the VCF bundle. VMware had some great demos showing persona-based execution of workflows which are common within customers. These demos were the highlight of the show for me and showed some real thought about how different personas would interact with a series of VMware software to accomplish a task like data center migration, app modernization or micro-segmentation.
Hybrid cloud
In terms of "hybrid cloud" being a common software defined infrastructure spanning public and private clouds, this part of VMware's messaging has not changed but has certainly grown more mature. To back that point, VMware is doubling down on its partnership with AWS (Amazon Web Services), now going on five years, with continued development of their joint VMware Cloud on AWS solution. The innovations we are seeing here are bringing VMC (VMware Cloud) on AWS into feature parity with the VMware on-prem suite through consumption-based offerings of all your favorite operational tools by way of the VMware Cloud Services console as well as feature updates around improving AWS native networking integrations, enabling VMware Tanzu for containerized services and the latest NSX developments for next-generation security and load balancing. VMware Cloud Disaster Recovery, a Recovery-as-a-Service solution based on VMC on AWS that simplifies disaster recovery operations while improving recovery times for protected workloads, also continues to see improvements though some of the most exciting ones will have to wait to be discussed later.

All that is not to say that VMware is leaving their other cloud partners out in the cold. Prior to EMPOWER, VMware added Google Cloud VMware Engine to the slate of solutions that may be purchased under the VMware Cloud Universal banner giving customers another way to consume it. I expect there will be similar announcements made soon around other VMware-as-a-Service offerings, potentially to include Azure VMware Solution which also gets a lot of mentions in these discussions. VMware's goal is to help customers get their workloads into all these cloud environments as quickly and as painlessly as possible so that customers can begin taking advantage of the more unique and differentiated cloud service provider offerings without having to upskill on other IaaS (Infrastructure as a Service) and PaaS (Platform as a Service) platforms and their supporting casts of new operational tools.
To that end, VMware is showcasing integrations between tools like vRealize Operations and vRealize Network Insight with their HCX migration tool to make customers' cloud migrations as simple, and even automated, as possible by not only removing the headaches of internetworking complexities, but also helping customers right-size workloads, plan migration waves and secure workloads as soon as they are moved.
Dev platforms
In response to feedback from customers and the field, VMware has been making efforts to simplify the messaging around the Tanzu Suite while continuing to add new capabilities. When faced with a decision between Tanzu Basic, Standard, and Advanced, customers were struggling to address gaps in functionality for either the operations or developers. The functionality of those suites also crossed lines of business, compounding the issue at hand with complexities around purchasing. EMPOWER 2022 was the place to see the fruits of their labor.
The Dev side of the DevOps coin can be summed up as "How do I get my app from code to production?" and Tanzu Application Platform (TAP) is the answer to that question. TAP provides a 'pre-paved path to delivery' for modern applications and makes the journey from code to production far easier. The biggest challenge with Developer Platforms is developer satisfaction. It seems elementary, but if you don't provide developers with what they asked for adoption will suffer. TAP was designed as a pluggable architecture, allowing developers to work with their preferred tools. Extending this architecture is a wealth of pre-configured templates and access to approved APIs (Application Programming Interfaces). This is how TAP enables developers to not only immediately begin developing code, but also accelerates the processes of iteration and debugging.
As mentioned in other sections of this article, multi and hybrid-cloud remain top of mind across the industry, and the need to develop apps that fit those models is clear. Compounding this issue is the need to adopt a shift-left, security-everywhere approach. TAP's application-aware design alleviates some of these burdens, allowing developers to increase their focus on defining the application requirements and the business logic. TAP automatically applies the best practices for the destination platform, promoting shift-left and app portability.

The Ops side of the DevOps coin is "Where is this app going to land and be run?" and Tanzu for Kubernetes Operations (TKO) is the answer here. Kubernetes is the new IaaS, operating as the new, standardized layer of abstraction across environments. But despite K8s increasing its already large advantage in market share with more customers than ever running K8s in production, challenges remain. Customers' primary concerns are centered around the expertise needed to deploy and maintain K8s Container Platforms and the need to ensure compliance and security requirements are met. A single glance at the CNCF (Cloud Native Computing Foundation) Landscape is all one needs to see the vast number of options in this space and the daunting nature of making the correct choices and integrations.
TKO addresses these challenges by being an opinionated starting point for a Kubernetes container platform. Focused on real-world use cases and honed by customer feedback, TKO provides the right components assembled under a reference architecture for multiple deployment methods. The goal here is to accelerate the establishment of a safe landing zone for your modern applications and enable that platform capability within your company. That capability needs the same shift-left, security-everywhere approach adopted with TAP, and both security and observability are cornerstones of TKO.
The combination of TAP and TKO aim to provide a Container-as-a-Service (CaaS) experience that is easier to operationalize while being adaptable to the needs of your organization and able to grow with you on your journey to the cloud.
SDN / Security
During EMPOWER 2022, VMware put forward a unified security message where security can be seen front and center within all their product offerings. VMware's security initiative focuses on two principal areas.
- Multicloud security
- Modern application security
Multicloud security
When VMware refers to multicloud security, they are referring to an organization's data center whether on-premises, in the cloud or a hybrid of the two. This aligns with VMware's other strategic initiative of any cloud, and device, anywhere.
VMware's ESXi hypervisor provides a unique opportunity to deploy distributed security applications at the Virtual Network Interface (VNIC) level of each workload through NSX-T with security features such as the Distributed Firewall (DFW), Intrusion detection systems / intrusion prevention systems (IDS/IPS), Network Traffic Analysis (NTA), Network Detection and Response (NDR), and sandboxing. All these security tools can be integrated within an existing data center without the need to hairpin traffic, make network changes, or re-IP workloads as can be the case with traditional security solutions. By using micro-segmentation through the implementation of the DFW, known good traffic can be allowed through and all other traffic can be blocked. Bad actors within an environment, leveraging allowed traffic protocols can be detected and stopped through signature-based analysis via the IDS/IPS and behavioral based analysis through Network Traffic Analysis (NTA) and Network Detection and Response (NDR).
Security policies throughout the security stack follow workloads across data centers and new workloads can automatically inherit security policies to ensure a consistent security posture is maintained.
Modern application security
Modern applications are not built like the virtual machines of today. Pods can be secured throughout the development lifecycle. Beginning with the container image, only approved golden images can be deployed. Once deployed, pod network traffic is protected both north/south as well as east/west by protecting API (Application Programmable Interface) endpoints via Envoy via API analysis. In addition, micro-service communication is protected through encryption via Tanzu Service Mesh in conjunction
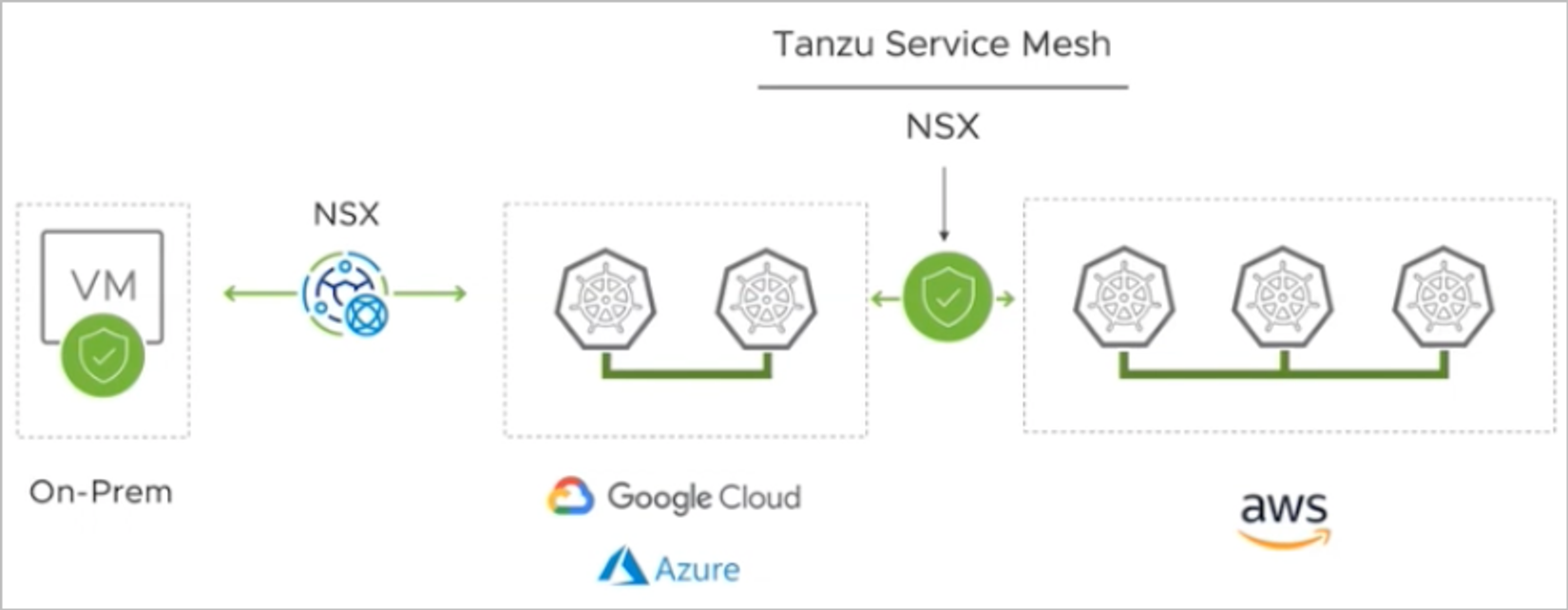
with Antrea, which is the Container Network Interface that provides stateful firewall protection via NSX-T DFW policies. By integrating NSX security features within a micro-services environment, companies can create security polices applied both to intra communication within a modern application deployment as well as inter communication within the larger data center, either on-premises or in the cloud.
VMware has made clear security is a strategic initiative with their "One VMware" push toward security everywhere. Their commitment to drive security as an important vertical is clear in their presentations, demos and features being brought to market.
Project Monterey (DPUs)
Project Monterey combines SR-IOV/Passthrough and Enhanced Data Path (EDP) and the benefits of both. SR-IOV allows for bypassing the vSwitch, but blocks all vSphere High Availability options. EDP uses VMXNET3 to abstract network from individual NIC (Network Interface Card) vendors while supporting all vSphere HA (High Availability) options.
Each host has a Data Processing Unit (DPU - SmartNIC) installed. VMware then installs a copy of ESXi on that DPU and because it is independent of the x86 CPU, the OS can use ESXi, Windows, or Linux allowing customers to leverage bare metal deployments. Initially the DPU will offload NSX traffic so it will not hit the CPU (Central Processing Unit) of the host, and this provides an added Security Isolation layer.
Future updates look to offload vSAN as well as security tasks to the DPU. The outstanding question for this technology is, will running DPUs save money by not having to purchase high end CPU, or will it just transition that cost from the CPU to the DPU?
Why WWT and VMware?
We have extensive experience within the VMware ecosystem and dedicated subject matter experts for all VMware solutions. When combined with the capabilities of our architects, we can deliver holistic solutions for our customers' digital transformations, making the impossible, possible.
Our Advanced Technology Center (ATC) allows us to test these solutions in controlled lab environments. Within the ATC, we record project outcomes in environments that mimic that of the customer. We perform very complex proofs of concept and proofs of value for VMware solutions, allowing for testing and modifications in a controlled environment prior to rolling out new initiatives across our customers' organizations.
Join the WWT Digital Platform today to start your digital transformation.